
Thanks to the fact that Linux is open-source, it is one of the most secure operating systems available. However, it is not perfect—like any software, it is open to exploits and there is a lot that can be done to improve its security. Improving the operating system is not just for experienced users—there are some simple things that everyone can do to make Ubuntu Linux more secure.
Encrypt Your Hard Drive
While a strong password is important for keeping your computer locked, it is not a foolproof way to keep your files secure—an experienced Linux user can access the files from a stolen laptop without a password. However, encrypting your hard drive makes it so that the password is not just a key to your computer but a code that is essential to accessing your files—without the password, any files that a hacker steals are impossible to read.
Unlike the other tips in this article, full hard drive encryption must be done during Ubuntu’s installation—while it is possible to encrypt partitions after installation, it is not as straightforward—plus, it is not all-encompassing like full hard drive encryption.
Below, we have a brand new image of Ubuntu 22.04. When you boot up your machine, whether it be on a physical device or a virtual machine, follow the set up as normal until you reach the screen shown below:
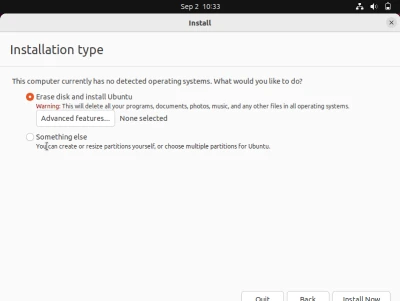
After reaching this screen, make sure to click on the “advanced features” option under “Erase disk and install ubuntu”. Once you do so, you should be greeted with the following screen:
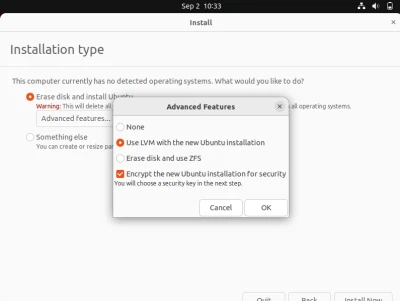
Once the advanced features menu opens up, make sure to select the “Use LVM…” option as well as the Encryption option. Once you do so, hit OK and click the Install Now option. Afterwards, you should see a screen similar to the one below:
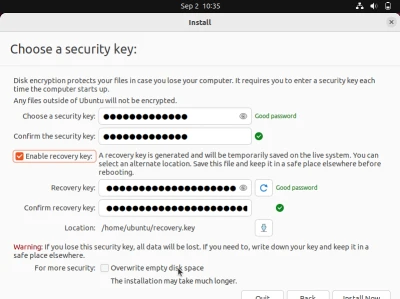 Here, we want to establish a security key as well as a recovery key in case you forget the initial security key. For additional security, you can overwrite the empty disk space and being that this is all done at installation, your disk should be empty.
Here, we want to establish a security key as well as a recovery key in case you forget the initial security key. For additional security, you can overwrite the empty disk space and being that this is all done at installation, your disk should be empty.
Once you have that all set up, you can continue with installation as normal and you should be all set, you now have disk encryption enabled!
Update your Operating System Regularly
While operating system updates are seen as a nuisance by many, keeping an operating system up to date is one of the most important measures that can be done to keep a system safe. A perfect example of the dangers of out-of-date software is the infamous WannaCry attack, in which a North Korean ransomware infected over 200,000 computers and caused hundreds of millions of dollars in damages in 2017. WannaCry only affected Windows computers that did not have the latest security update. While not all of the widely used versions of Windows had this update available, according to research from the Kaspersky Lab, 98% of users affected by WannaCry were using Windows 7, which did have the security update available. If these users simply updated their computers, they would not have been affected by one of the largest ransomware attacks.
While Linux is generally more secure than Windows, it is just as important to regularly update Linux. Since Linux is open-source, anyone can search its code for bugs and help to fix them. This means that once an exploit in Linux is found, it will generally be fixed quickly, but it also means that it is important to update as soon as possible because the exploit will be known to the public.
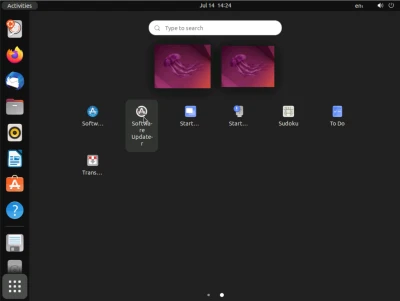
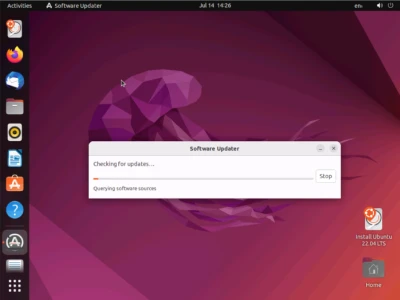
The easiest way to update Ubuntu is to run the software updater application.
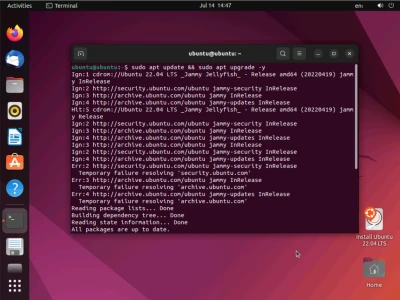
To update via the terminal, enter the command “sudo apt update && sudo apt upgrade -y.”
Disable Root Access
Linux is a command-heavy operating system—while an average user can use Linux and never see the terminal, it is still a powerful tool that can potentially give attackers full access to a computer. The unrestricted ability to run any command in Linux is known as “root access,” and can be safely disabled since it is not really needed most of the time. If root access is ever needed, it can always be locked behind a password.
To lock root access behind a password, open the terminal and enter “sudo -i.” When the next line, a # prompt, appears, enter “password.” This will give you the prompt for setting a root password.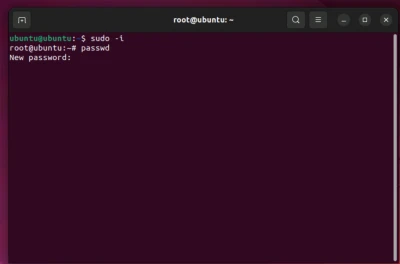
Disable unnecessary services
Because Linux has been around for so long, it contains many leftover features that are outdated and no longer necessary. If allowed to run, these features can be a security flaw, especially if they provide access to ports.
To list all services that are running in Linux, open the command line. See the below resources for more information on this:
Safe Internet Browsing
Nowadays, most browsers make a profit by selling their users’ data to advertisers. While this is usually unnoticeable by users, allowing websites to install data-collecting third-party cookies can make users open to attacks, phishing, and identity theft.
Ubuntu comes with Firefox installed as the default browser. While Firefox is already a great browser for privacy, it is always good to disable third-party cookies. Additionally, browser extensions such as Adblock, HTTPS Everywhere, and NoScript can help make browsing the internet more secure.
Adblock
Adblock extensions disable advertisements on websites, making browsing the internet easier by hiding obstructing ads. They also prevent users from seeing malicious scam advertisements and disable third-party cookies. Popular adblock extensions include Adblock, AdBlock Plus, and uBlock Origin.
HTTPS Everywhere
Even though most people do not write “ before URLs anymore, the Hypertext Transfer Protocol is still used to connect to every website. Since 2008, websites have started to switch to the Hypertext Transfer Protocol Secure, or HTTPS, which encrypts traffic between the user and the site, and sites that only use HTTP are considered insecure. HTTPS Everywhere automatically switches HTTP connections to HTTPS connections whenever it is available, helping keep internet traffic safer.
NoScript
While websites are still primarily built using HTML and CSS, they often have a lot of behind-the-scenes code written in languages such as JavaScript and Java. While there are many legitimate uses for these scripts, they are also one of the main tools used by malicious sites and hackers to run malware. NoScript disables scripts that are not from sites that users declare that they trust.
Conclusion
While Linux is a secure operating system by default, its ability to be customized allows for a multitude of ways to make it more secure. Making Linux more secure is something that anyone, not just cybersecurity experts, can and should do for the best and safest experience.
















